In our modern lives, we store so much information online, whether it be personal information or important business information. If this information gets into the wrong hands, it can cause you or your business huge issues.
However, you can take steps to prevent attackers from getting your information, by purchasing security keys. The good news is security keys can provide a high level of security, and are becoming more affordable.
We have done the hard work and found you 5 of the best security keys available.
1. YubiKey 5 NFC

The YubiKey 5 NFC is the world’s number 1 multi-protocol security key product. It has strong phishing defence capabilities, which stops account takeovers. A range of authentication choices is available, including passwordless authentication, and a seamless touch-to-sign-in process. It can be scaled up to use for individual users for personal use right up to the largest international organizations.
2. YubiKey 5 NFC FIPS
3. Security Key NFC by Yubico

This product provides an easy tap-and-go security key for any NFC-enabled Android, Windows 10, or iOS device. This security key is made from fibreglass, which protects it from day-to-day use, which is great for those who want a security key for travelling. If you are interested in purchasing this product, you should be aware that this key does not work with the company’s Authenticator App.
4. YubiKey Bio - FIDO Edition
5. YubiHSM 2
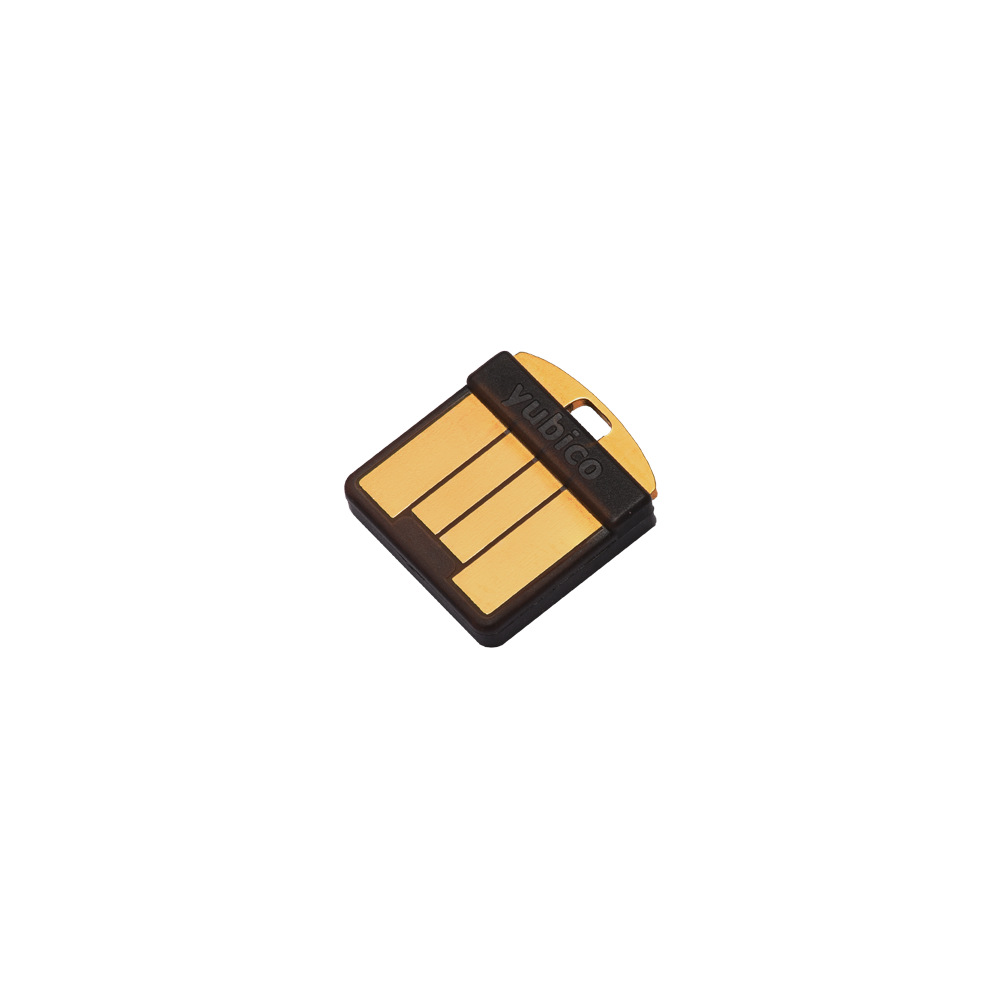
The YubiHSM 2 is a game-changing security product. It is used purely for businesses and stops attackers from copying your Certificate Authority root keys. It is most commonly used with digital signature generation and certification, but it is increasingly being used to secure cryptocurrency exchanges and IoT gateways.